Vulnerability Assessment & Penetration Testing
VA & PT
Vulnerability Assessment & Penetration Testing
Vulnerability Assessment & Penetration Testing offers your company a chance to uncover vulnerabilities that are most likely to be used by cyber adversaries to carry out infiltration.
With our risk-based penetration assessment services, you can keep your data safe from a malicious user who wants to get access to sensitive information without appropriate permissions.
Reduce Risk, Achieve Cyber Resiliency
Choose the advanced Pen Testing and Cyber Security Services for Your Business
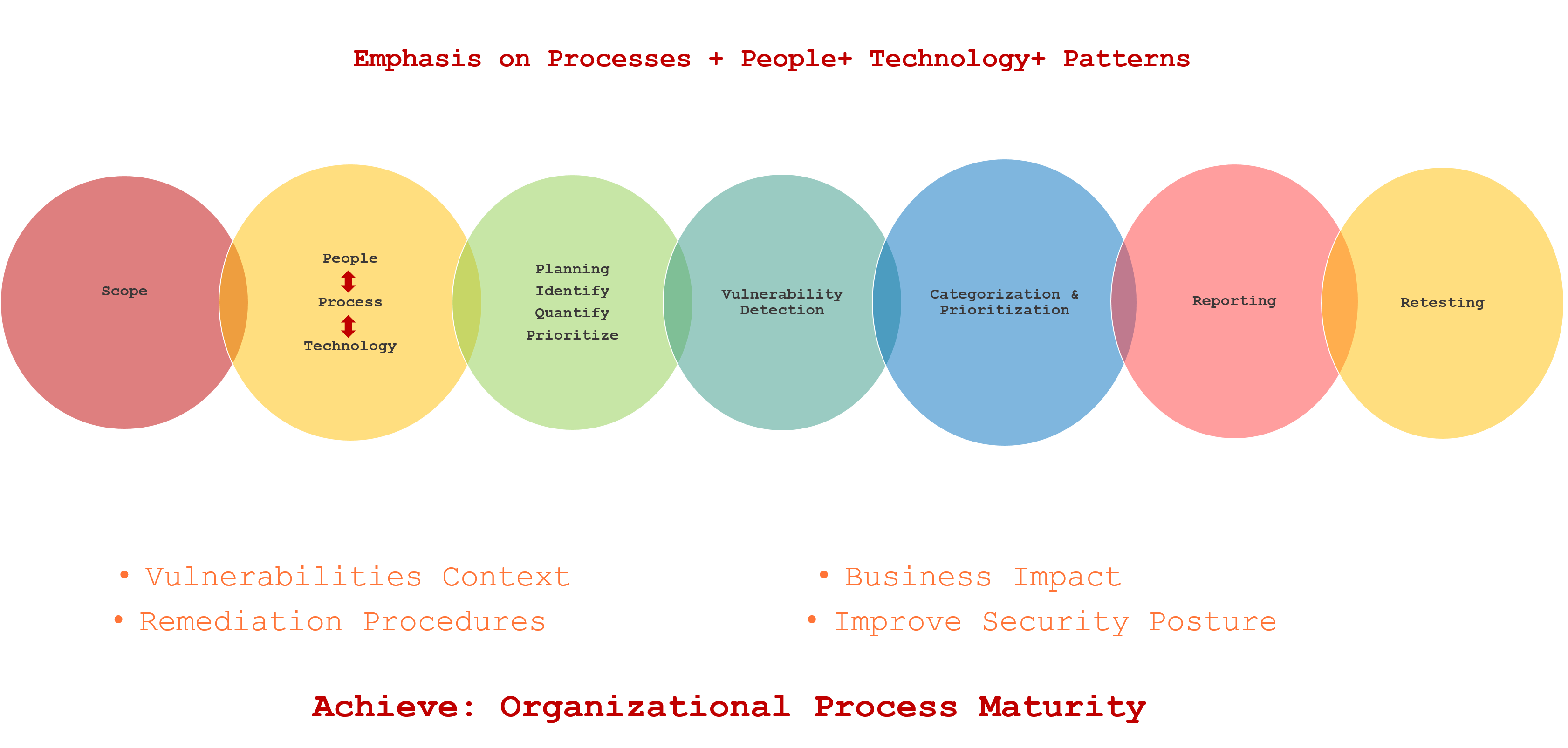
Planning & Defining Objective
The first stage involves defining and documenting test objectives, scope, and rules of engagement.
Remediation Testing
Once vulnerabilities are established and remediated, CSI as the best cyber security services company runs a re-test on your networks and systems to confirm that fixes were effectively instigated and ascertain any new vulnerabilities that might be identified due to remediation.
Information Gathering
During the reconnaissance phase, Cyber Security inc. gathers and analyzes important data about the under attack application and related infrastructure.
Vulnerability Detection
A vulnerability assessment is conducted to recognize any security flaws through research, testing, and validation.
Analyze findings
This is the last phase of cyber security penetration testing. In this phase, our experts dig deeper into all the identified vulnerabilities to ascertain the actual risk level of the potential attack on your networks and systems and try to minimize false-positive results.
Reporting
Once the process of analyzing your vulnerabilities is completed, we will provide our customers with a detailed comprehensive report stating findings and the recommendations to prioritize and fix the results along with the customer.
Previous slide
Next slide
